Virtual CISO Market Size, By Region (North America, Europe, Asia-Pacific, Latin America, Middle East and Africa), By Statistics, Trends, Outlook and Forecast 2026 to 2033 (Financial Impact Analysis)
ID : MRU_ 444706 | Date : Feb, 2026 | Pages : 248 | Region : Global | Publisher : MRU
Virtual CISO Market Size
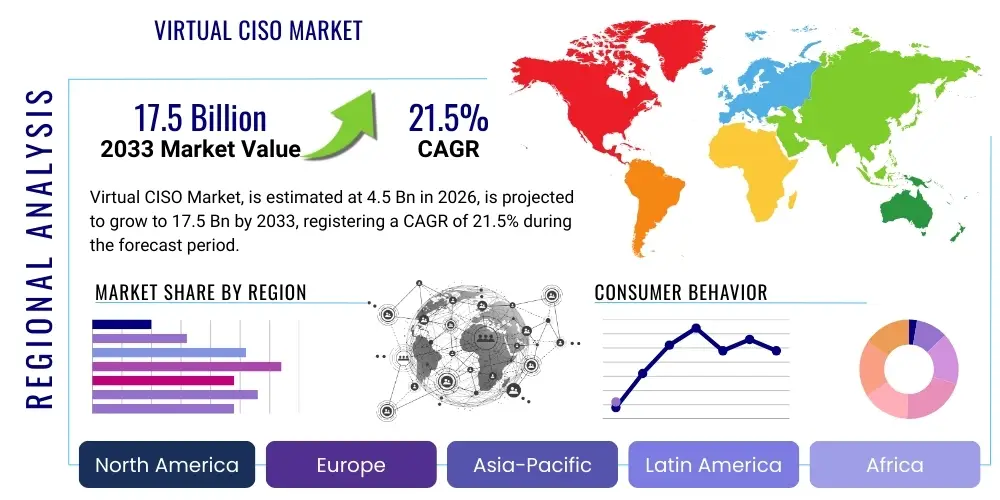
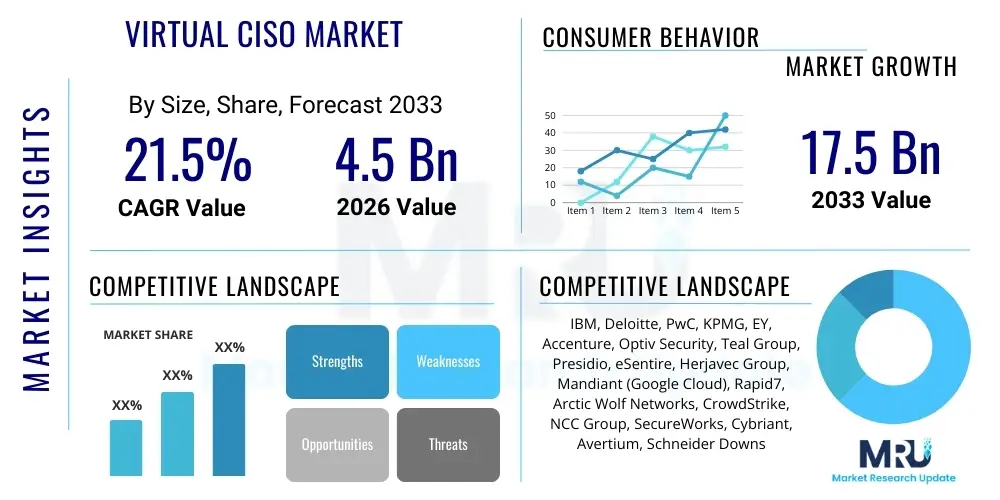
The Virtual CISO Market is projected to grow at a Compound Annual Growth Rate (CAGR) of 21.5% between 2026 and 2033. The market is estimated at USD 4.5 Billion in 2026 and is projected to reach USD 17.5 Billion by the end of the forecast period in 2033.
Virtual CISO Market introduction
The Virtual Chief Information Security Officer (vCISO) market is experiencing robust expansion, driven by the escalating complexity of the cyber threat landscape and the increasing regulatory demands placed on organizations of all sizes. A vCISO service offers organizations access to high-level cybersecurity expertise on a flexible, part-time, or on-demand basis, eliminating the need for a full-time, in-house executive. This model provides strategic guidance, risk management, and compliance oversight, akin to a traditional CISO, but delivered remotely or through a hybrid approach by external security professionals. Major applications span across various sectors, including financial services, healthcare, IT and telecom, and critical infrastructure, where robust cybersecurity postures are paramount. The primary benefits include cost-effectiveness, access to a broad spectrum of specialized knowledge, scalability, and enhanced agility in responding to evolving cyber threats without the overhead of a senior executive salary and benefits. Key driving factors propelling this market forward encompass the global shortage of skilled cybersecurity professionals, the continuous evolution of sophisticated cyberattacks, stringent data protection regulations such as GDPR and CCPA, and the accelerated adoption of cloud computing and digital transformation initiatives that expand attack surfaces. These elements collectively underscore the indispensable role of expert cybersecurity leadership that the vCISO model proficiently delivers.
Virtual CISO Market Executive Summary
The Virtual CISO market is characterized by dynamic business trends reflecting a heightened awareness of cybersecurity as a board-level imperative, moving beyond a purely IT function. Enterprises are increasingly prioritizing strategic cybersecurity planning, risk posture improvement, and compliance adherence, often facilitated by external vCISO experts who bring diverse industry experience and best practices. Regional trends indicate strong growth in North America and Europe, fueled by mature regulatory environments and a high concentration of digitally transformed businesses, while the Asia Pacific region is rapidly emerging as a significant market due to rapid digitalization and expanding regulatory frameworks. Segmentation trends highlight a growing demand from Small and Medium-sized Enterprises (SMEs) that often lack the resources for a full-time CISO, along with a specialized demand from highly regulated industries such as healthcare and financial services for tailored compliance expertise. The market is also witnessing a shift towards more comprehensive service offerings that integrate advanced threat intelligence, incident response planning, and cloud security consulting. This executive overview encapsulates a market poised for sustained expansion, driven by continuous cyber innovation, evolving regulatory landscapes, and the increasing recognition of cybersecurity as a fundamental business enabler rather than merely an operational cost.
AI Impact Analysis on Virtual CISO Market
Users frequently inquire about how artificial intelligence will reshape the role of the Virtual CISO, expressing curiosity about AI's potential to automate tasks, improve threat detection, and enhance overall security posture, while also voicing concerns regarding data privacy, ethical implications, and the potential for AI to introduce new vulnerabilities or algorithmic biases. Many questions revolve around whether AI will augment or ultimately replace human vCISOs, emphasizing the desire to understand how AI tools can be integrated to create a more proactive and resilient security framework. There is a clear expectation that AI will provide more sophisticated insights and automation, thereby empowering vCISOs to focus on higher-level strategic decision-making and human-centric challenges rather than getting bogged down in routine operational tasks. The overarching theme is one of leveraging AI as a force multiplier, optimizing existing security processes and offering predictive capabilities that were previously unattainable, while simultaneously managing the inherent risks associated with advanced technological adoption in sensitive security domains. Ultimately, users seek clarity on the practical applications and strategic advantages AI can bring to the vCISO service model, alongside a realistic appraisal of its limitations and the necessary human oversight.
- Enhanced Threat Intelligence: AI algorithms can analyze vast datasets of threat indicators, vulnerabilities, and attack patterns to provide vCISOs with proactive, context-rich threat intelligence, enabling faster identification of emerging risks and more precise defensive strategies.
- Automated Vulnerability Management: AI-powered tools can automate the scanning, prioritization, and remediation of vulnerabilities across an organization's digital assets, significantly reducing the manual effort required and allowing vCISOs to focus on critical strategic security initiatives.
- Predictive Analytics for Risk Assessment: Leveraging machine learning, AI can predict potential security breaches and identify high-risk areas based on historical data and real-time network behavior, offering vCISOs a data-driven approach to risk assessment and resource allocation.
- Faster and More Accurate Incident Response: AI can accelerate the detection and analysis of security incidents by identifying anomalies and correlating events across disparate systems, enabling vCISOs to orchestrate quicker containment, eradication, and recovery efforts.
- Improved Compliance Monitoring and Reporting: AI can automate the continuous monitoring of regulatory compliance, flagging deviations from policies and generating comprehensive audit-ready reports, thereby streamlining a critical and often time-consuming vCISO responsibility.
- AI-driven Security Awareness Training: AI can personalize security awareness training modules based on individual user behaviors and vulnerabilities, making educational programs more effective and improving the overall human firewall within an organization, a key component of a vCISO's strategy.
- Optimization of Security Operations: AI-powered Security Orchestration, Automation, and Response (SOAR) platforms can automate repetitive security tasks, integrate various security tools, and standardize workflows, freeing up vCISOs to concentrate on strategic planning and complex problem-solving.
- Data Privacy and Governance Enhancement: AI can assist vCISOs in classifying sensitive data, monitoring data access patterns, and ensuring compliance with data privacy regulations by identifying and alerting on potential policy violations across an organization's data landscape.
- Supply Chain Risk Management: AI tools can analyze third-party vendor security postures and detect potential risks within the supply chain, providing vCISOs with crucial insights for managing external dependencies and safeguarding the broader organizational ecosystem.
DRO & Impact Forces Of Virtual CISO Market
The Virtual CISO market is significantly shaped by a confluence of Drivers, Restraints, and Opportunities, amplified by various Impact Forces. Key Drivers include the exponential rise in sophisticated cyberattacks, creating an urgent demand for expert cybersecurity leadership that many organizations lack internally. The growing complexity of global data privacy and security regulations (e.g., GDPR, CCPA, HIPAA) mandates specialized compliance expertise, which vCISOs proficiently provide. Furthermore, the persistent global shortage of qualified cybersecurity professionals makes the vCISO model an attractive, cost-effective alternative to hiring a full-time CISO, especially for Small and Medium-sized Enterprises (SMEs) that cannot justify the expense of a dedicated executive. On the other hand, Restraints to market growth include ongoing concerns about data privacy and the security of sensitive information when outsourcing such critical functions to third-party providers. A potential over-reliance on external consultants might also raise questions about internal capability development and knowledge transfer. Standardizing service level agreements and ensuring consistent quality across diverse vCISO providers remains a challenge, particularly for organizations seeking tailored solutions. Budgetary constraints for smaller firms, despite the cost-effectiveness, can still pose a barrier to adopting comprehensive vCISO services. Opportunities abound with the rapid integration of artificial intelligence and machine learning into cybersecurity tools, enabling vCISOs to deliver more proactive and predictive security strategies. The expansion into niche vertical markets requiring highly specialized compliance and security knowledge, such as critical infrastructure or industrial control systems, presents significant growth avenues. Strategic partnerships between vCISO providers and technology vendors can create integrated solutions, enhancing service offerings and market reach. The increasing adoption of hybrid work models further necessitates robust remote security strategies, a core competence of vCISOs. Impact Forces such as technological advancements, particularly in cloud security and zero-trust architectures, continually reshape the service landscape, requiring vCISOs to stay at the forefront of innovation. Regulatory changes and geopolitical tensions, which often manifest as increased state-sponsored cyber threats, directly influence the demand for enhanced security oversight. Economic conditions dictate enterprise spending on cybersecurity, while the evolving threat landscape, characterized by ransomware, supply chain attacks, and advanced persistent threats, consistently reinforces the criticality of expert security guidance, thereby propelling the vCISO market forward as an essential component of modern enterprise risk management.
Segmentation Analysis
The Virtual CISO market is comprehensively segmented to cater to the diverse needs of its clientele, reflecting various organizational structures, operational scales, and industry-specific requirements. This segmentation allows providers to offer highly tailored services, optimizing resource allocation and enhancing the value proposition for different market verticals. Analysis typically considers factors such as the size of the organization, the specific industry vertical, the type of services required, and the preferred deployment model for service delivery. Understanding these distinct segments is crucial for both market entrants and established players to identify high-growth areas, develop specialized offerings, and refine their go-to-market strategies, ultimately driving market penetration and competitive advantage. The intricate interplay between these segmentation criteria underscores the dynamic and evolving nature of the cybersecurity services landscape, where flexibility and customization are key to sustained success and client satisfaction.
- By Organization Size:
- Small and Medium-sized Enterprises (SMEs): Organizations with limited in-house cybersecurity resources and budget constraints.
- Large Enterprises: Corporations requiring highly specialized, scalable, and often global cybersecurity expertise to complement existing security teams or drive specific projects.
- By Industry Vertical:
- BFSI (Banking, Financial Services, and Insurance): Highly regulated sector with stringent compliance and data protection requirements.
- Healthcare: Critical infrastructure sector handling sensitive patient data, subject to strict regulations like HIPAA.
- IT & Telecom: Industries at the forefront of technology, facing complex and constantly evolving cyber threats.
- Government & Public Sector: Entities requiring robust security for critical national infrastructure and citizen data.
- Retail & E-commerce: Businesses managing vast amounts of customer data and online transaction security.
- Manufacturing: Increasingly reliant on IoT and operational technology (OT), prone to industrial espionage and disruption.
- Energy & Utilities: Critical infrastructure sector vulnerable to state-sponsored attacks and operational disruptions.
- Others: Includes media & entertainment, education, legal, and professional services, each with unique security needs.
- By Service Type:
- Security Program Development: Establishing foundational cybersecurity policies, frameworks, and strategies.
- Risk Management: Identifying, assessing, and mitigating cybersecurity risks across the organization.
- Compliance Management: Ensuring adherence to industry-specific and global regulatory requirements.
- Incident Response & Recovery: Developing and executing plans for managing and recovering from security breaches.
- Security Awareness Training: Educating employees on best practices and threat recognition to strengthen the human firewall.
- Cloud Security Consulting: Providing expert guidance on securing cloud environments and applications.
- Data Privacy & Protection: Strategies and implementation for safeguarding sensitive data against unauthorized access and breaches.
- Vendor Risk Management: Assessing and managing the cybersecurity risks associated with third-party vendors and supply chains.
- By Deployment Model:
- Remote: Services delivered entirely off-site by vCISO professionals.
- Hybrid: A blend of remote support with occasional on-site presence for critical meetings or assessments.
- On-site (Part-time Strategic Presence): Less common for pure "virtual," but includes models where a vCISO might spend a predefined, limited number of days on-site for strategic oversight.
Value Chain Analysis For Virtual CISO Market
The Value Chain Analysis for the Virtual CISO Market illustrates the sequence of activities that transform raw security intelligence and expertise into delivered value for clients. This chain begins with upstream activities, which involve the aggregation of raw threat intelligence, the continuous development of cybersecurity frameworks, methodologies, and proprietary tools, as well as the recruitment and specialized training of highly skilled cybersecurity professionals. Upstream providers might include threat intelligence platforms, security software vendors, and educational institutions contributing to the talent pool. These foundational elements are crucial for equipping vCISO providers with the necessary knowledge base and technological arsenal. Moving downstream, the value chain progresses through service delivery, which encompasses the initial client assessment, strategic planning, risk assessments, implementation of security policies, compliance monitoring, incident response coordination, and ongoing advisory services. This phase involves direct interaction with clients, understanding their unique business context, and tailoring security strategies to meet specific organizational needs and regulatory requirements. The efficiency and quality of service delivery are paramount at this stage, directly influencing client satisfaction and retention. Distribution channels for vCISO services are typically direct, through the vCISO firms' own sales teams and marketing efforts, allowing for bespoke solutions and direct client relationships. Indirect channels may involve partnerships with managed service providers (MSPs), IT consulting firms, or legal and compliance advisory practices that integrate vCISO services into their broader offerings, thereby expanding reach and complementing existing client relationships. Both direct and indirect channels play a vital role in connecting expertise with demand, ensuring that organizations can access the specialized cybersecurity leadership required to navigate today's complex threat landscape. The entire value chain emphasizes the continuous evolution of security practices, the leveraging of advanced technologies, and the strategic application of human expertise to create robust and resilient cybersecurity postures for diverse clientele.
Virtual CISO Market Potential Customers
The Virtual CISO market caters to a broad spectrum of potential customers, primarily categorized as End-Users or Buyers, who are seeking to enhance their cybersecurity posture, manage risks, and ensure compliance without the overhead of a full-time executive CISO. Small and Medium-sized Enterprises (SMEs) represent a significant segment, as they often lack the financial resources or internal expertise to employ a dedicated Chief Information Security Officer, yet face the same, if not greater, cybersecurity threats as larger corporations. These organizations are driven by the need for cost-effective access to expert guidance for regulatory compliance, data protection, and incident response planning. Mid-market companies also form a crucial customer base, as they navigate rapid growth, digital transformation, and increasing regulatory scrutiny, requiring scalable cybersecurity leadership that can adapt to evolving business needs. Furthermore, large enterprises sometimes engage vCISOs for specific projects, specialized expertise (e.g., cloud security, IoT security), or to augment an existing CISO team during periods of high demand or strategic initiatives. Highly regulated industries, such as Banking, Financial Services, and Insurance (BFSI), Healthcare, and Government agencies, are prime candidates due to their stringent compliance requirements (e.g., PCI DSS, HIPAA, GDPR) and the critical nature of the data they handle, making expert strategic security oversight indispensable. Technology companies, e-commerce platforms, and organizations heavily reliant on digital infrastructure also seek vCISO services to protect intellectual property, customer data, and ensure business continuity. Essentially, any organization that recognizes the critical importance of robust cybersecurity but faces challenges in acquiring or retaining top-tier, in-house security leadership is a potential customer for Virtual CISO services, making the market exceptionally diverse and expansive in its potential reach across various industries and organizational scales.
| Report Attributes | Report Details |
|---|---|
| Market Size in 2026 | USD 4.5 Billion |
| Market Forecast in 2033 | USD 17.5 Billion |
| Growth Rate | 21.5% CAGR |
| Historical Year | 2019 to 2024 |
| Base Year | 2025 |
| Forecast Year | 2026 - 2033 |
| DRO & Impact Forces |
|
| Segments Covered |
|
| Key Companies Covered | IBM, Deloitte, PwC, KPMG, EY, Accenture, Optiv Security, Teal Group, Presidio, eSentire, Herjavec Group, Mandiant (Google Cloud), Rapid7, Arctic Wolf Networks, CrowdStrike, NCC Group, SecureWorks, Cybriant, Avertium, Schneider Downs |
| Regions Covered | North America, Europe, Asia Pacific (APAC), Latin America, Middle East, and Africa (MEA) |
| Enquiry Before Buy | Have specific requirements? Send us your enquiry before purchase to get customized research options. Request For Enquiry Before Buy |
Virtual CISO Market Key Technology Landscape
The Virtual CISO market leverages a sophisticated and continually evolving technology landscape to deliver comprehensive cybersecurity services, enabling proactive defense, efficient risk management, and robust compliance adherence. At the core of this landscape are advanced Security Information and Event Management (SIEM) systems and Security Orchestration, Automation, and Response (SOAR) platforms, which collect, analyze, and correlate security data from various sources, facilitating rapid threat detection and automated incident response workflows. Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platforms (CWPP) are critical for vCISOs overseeing organizations with significant cloud footprints, ensuring configurations are secure and workloads are protected across multi-cloud environments. Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) solutions provide deep visibility into endpoint activities and broader security telemetry, empowering vCISOs to identify and contain advanced threats that bypass traditional defenses. Identity and Access Management (IAM) systems, including multi-factor authentication (MFA) and privileged access management (PAM), are fundamental for controlling who has access to what resources, a cornerstone of zero-trust architectures championed by modern vCISOs. Governance, Risk, and Compliance (GRC) platforms are essential tools that enable vCISOs to manage regulatory requirements, conduct risk assessments, and streamline audit processes, providing a centralized framework for demonstrating due diligence. Furthermore, threat intelligence platforms feed real-time, actionable insights into emerging threats and vulnerabilities, allowing vCISOs to make informed strategic decisions. Data Loss Prevention (DLP) solutions help protect sensitive information from exfiltration, while Vulnerability Management (VM) platforms continuously identify and prioritize security weaknesses. The integration of Artificial Intelligence (AI) and Machine Learning (ML) is becoming increasingly prevalent across all these technologies, enhancing capabilities in anomaly detection, predictive analytics, and automated response. These AI/ML-driven tools enable vCISOs to manage vast amounts of security data more effectively, identify subtle threat patterns, and streamline labor-intensive tasks, thereby amplifying their strategic impact. Secure Access Service Edge (SASE) frameworks integrate networking and security functions into a single cloud-native service, crucial for supporting distributed workforces and protecting data at the edge. Cryptographic technologies, including advanced encryption standards and secure key management systems, are also vital for data protection in transit and at rest. Together, these technologies form a powerful ecosystem that enables virtual CISOs to provide cutting-edge, scalable, and adaptive cybersecurity leadership, effectively safeguarding client assets against an ever-more sophisticated array of cyber threats while ensuring operational resilience and regulatory compliance. The continuous innovation in these technological domains directly fuels the efficacy and expanding scope of virtual CISO services, positioning them as indispensable partners in today's digital economy.
Regional Highlights
- North America: Dominates the Virtual CISO market due to a high concentration of technologically advanced companies, stringent regulatory frameworks like HIPAA and CCPA, and a robust cybersecurity awareness culture. The region benefits from a significant shortage of in-house cybersecurity talent, driving demand for outsourced expertise. Major growth is observed in the United States and Canada, where industries such as BFSI, healthcare, and IT heavily invest in strategic security guidance.
- Europe: Represents a substantial market share, primarily driven by comprehensive data protection regulations such as GDPR, which mandate robust cybersecurity and data privacy practices across all sectors. Countries like the UK, Germany, France, and the Netherlands are key contributors, exhibiting strong adoption of vCISO services by both large enterprises and a growing number of SMEs aiming to achieve compliance and improve cyber resilience.
- Asia Pacific (APAC): Expected to witness the highest growth rate, propelled by rapid digitalization initiatives, increasing cloud adoption, and a burgeoning threat landscape. Emerging economies like India, China, Japan, Australia, and Singapore are rapidly enhancing their digital infrastructure, leading to a surge in demand for expert cybersecurity leadership. Regulatory developments and growing awareness among local businesses are further accelerating market expansion.
- Latin America: Shows promising growth, albeit from a smaller base, driven by increasing internet penetration, digital transformation efforts, and a rising recognition of cybersecurity risks. Countries like Brazil, Mexico, and Argentina are gradually adopting vCISO services as organizations seek to mature their security postures and comply with evolving regional data protection laws, often against a backdrop of limited internal resources.
- Middle East and Africa (MEA): This region is experiencing steady growth, fueled by government-led digital transformation agendas, significant investments in critical infrastructure, and an increased focus on diversifying economies beyond oil. Nations such as the UAE, Saudi Arabia, and South Africa are key markets, where organizations are increasingly leveraging vCISO services to secure their digital assets and build robust cybersecurity frameworks in line with international best practices and regional regulatory requirements.
Top Key Players
The market research report includes a detailed profile of leading stakeholders in the Virtual CISO Market.- IBM
- Deloitte
- PwC
- KPMG
- EY
- Accenture
- Optiv Security
- Teal Group
- Presidio
- eSentire
- Herjavec Group
- Mandiant (Google Cloud)
- Rapid7
- Arctic Wolf Networks
- CrowdStrike
- NCC Group
- SecureWorks
- Cybriant
- Avertium
- Schneider Downs
Frequently Asked Questions
Analyze common user questions about the Virtual CISO market and generate a concise list of summarized FAQs reflecting key topics and concerns.What is a Virtual CISO (vCISO) and how does it differ from a traditional CISO?
A Virtual CISO (vCISO) provides high-level cybersecurity expertise and strategic guidance to an organization on a part-time, flexible, or on-demand basis, typically from an external service provider. Unlike a traditional, full-time in-house CISO, a vCISO offers a cost-effective solution, leveraging a broad range of experience across multiple clients, without the need for a dedicated executive salary and benefits. The core function remains strategic security leadership, risk management, and compliance, but delivered with greater agility and scalability.
Why should my organization consider hiring a vCISO?
Organizations, particularly Small and Medium-sized Enterprises (SMEs), should consider a vCISO to gain access to expert cybersecurity leadership and strategic insights without the significant cost of a full-time Chief Information Security Officer. A vCISO helps navigate complex threat landscapes, ensures regulatory compliance (e.g., GDPR, HIPAA), improves overall security posture, and provides incident response planning, filling the gap caused by the global cybersecurity talent shortage and budget constraints.
What are the key benefits of implementing vCISO services for a business?
Implementing vCISO services offers several key benefits, including substantial cost savings compared to hiring a full-time CISO, immediate access to diverse and specialized cybersecurity expertise, and enhanced agility in adapting to evolving threats and regulations. Additionally, vCISOs provide objective, third-party perspectives, improve risk management and compliance, strengthen security awareness, and enable organizations to focus internal resources on core business functions while maintaining a robust security posture.
What specific services can a Virtual CISO provide?
A Virtual CISO can provide a comprehensive suite of services, including the development of robust cybersecurity strategies and policies, conducting thorough risk assessments and vulnerability management, and ensuring adherence to industry-specific and global compliance standards. They also play a crucial role in incident response planning and coordination, offer security awareness training for employees, provide expert guidance on cloud security, and manage third-party vendor risks, essentially covering all critical aspects of an organization's security program.
How does a vCISO ensure data privacy and regulatory compliance for clients?
A vCISO ensures data privacy and regulatory compliance by first conducting a thorough assessment of the client's current posture against relevant regulations like GDPR, CCPA, or HIPAA. They then develop and implement tailored policies, procedures, and controls, provide ongoing monitoring of security practices, and conduct regular audits to identify and remediate any non-compliance. Their expertise includes advising on data governance, privacy-by-design principles, and preparing organizations for external audits, thereby maintaining a strong and defensible compliance framework.
To check our Table of Contents, please mail us at: sales@marketresearchupdate.com
Research Methodology
The Market Research Update offers technology-driven solutions and its full integration in the research process to be skilled at every step. We use diverse assets to produce the best results for our clients. The success of a research project is completely reliant on the research process adopted by the company. Market Research Update assists its clients to recognize opportunities by examining the global market and offering economic insights. We are proud of our extensive coverage that encompasses the understanding of numerous major industry domains.
Market Research Update provide consistency in our research report, also we provide on the part of the analysis of forecast across a gamut of coverage geographies and coverage. The research teams carry out primary and secondary research to implement and design the data collection procedure. The research team then analyzes data about the latest trends and major issues in reference to each industry and country. This helps to determine the anticipated market-related procedures in the future. The company offers technology-driven solutions and its full incorporation in the research method to be skilled at each step.
The Company's Research Process Has the Following Advantages:
- Information Procurement
The step comprises the procurement of market-related information or data via different methodologies & sources.
- Information Investigation
This step comprises the mapping and investigation of all the information procured from the earlier step. It also includes the analysis of data differences observed across numerous data sources.
- Highly Authentic Source
We offer highly authentic information from numerous sources. To fulfills the client’s requirement.
- Market Formulation
This step entails the placement of data points at suitable market spaces in an effort to assume possible conclusions. Analyst viewpoint and subject matter specialist based examining the form of market sizing also plays an essential role in this step.
- Validation & Publishing of Information
Validation is a significant step in the procedure. Validation via an intricately designed procedure assists us to conclude data-points to be used for final calculations.
×
Request Free Sample:
Related Reports
Select License

Why Choose Us

We're cost-effective and Offered Best services:
We are flexible and responsive startup research firm. We adapt as your research requires change, with cost-effectiveness and highly researched report that larger companies can't match.

Information Safety
Market Research Update ensure that we deliver best reports. We care about the confidential and personal information quality, safety, of reports. We use Authorize secure payment process.

We Are Committed to Quality and Deadlines
We offer quality of reports within deadlines. We've worked hard to find the best ways to offer our customers results-oriented and process driven consulting services.

Our Remarkable Track Record
We concentrate on developing lasting and strong client relationship. At present, we hold numerous preferred relationships with industry leading firms that have relied on us constantly for their research requirements.

Best Service Assured
Buy reports from our executives that best suits your need and helps you stay ahead of the competition.

Customized Research Reports
Our research services are custom-made especially to you and your firm in order to discover practical growth recommendations and strategies. We don't stick to a one size fits all strategy. We appreciate that your business has particular research necessities.

Service Assurance
At Market Research Update, we are dedicated to offer the best probable recommendations and service to all our clients. You will be able to speak to experienced analyst who will be aware of your research requirements precisely.
Contact With Our Sales Team
Customer Testimonials
The content of the report is always up to the mark. Good to see speakers from expertise authorities.
Privacy requested , Managing Director
A lot of unique and interesting topics which are described in good manner.
Privacy requested, President
Well researched, expertise analysts, well organized, concrete and current topics delivered in time.
Privacy requested, Development Manager